The Growing Need for Real-Time Cyber Threat Detection
In an era where digital transformation is at the forefront of business strategies, cyber threats have become a pressing concern. With the increasing sophistication of cyber-attacks, organizations must pivot towards more proactive defense mechanisms. Implementing AI-driven tools for real-time cyber threat detection is not just an option but a necessity.
The Role of AI in Cybersecurity
Artificial Intelligence (AI) offers unprecedented opportunities to enhance cybersecurity measures. By leveraging machine learning algorithms, organizations can analyze vast amounts of data to identify patterns indicative of potential threats. This enables the detection of anomalies that traditional rule-based systems might overlook.
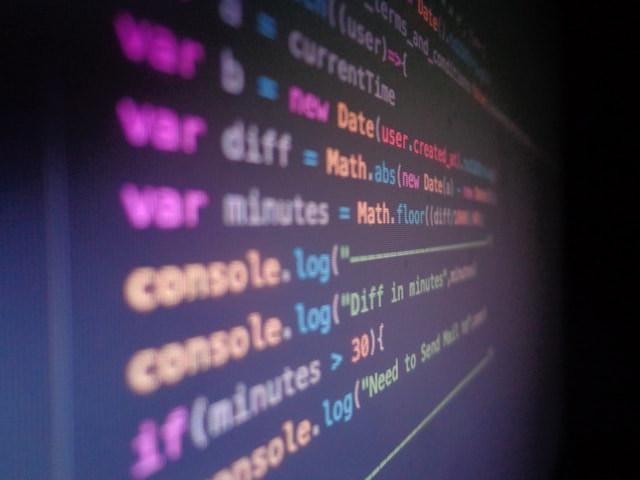
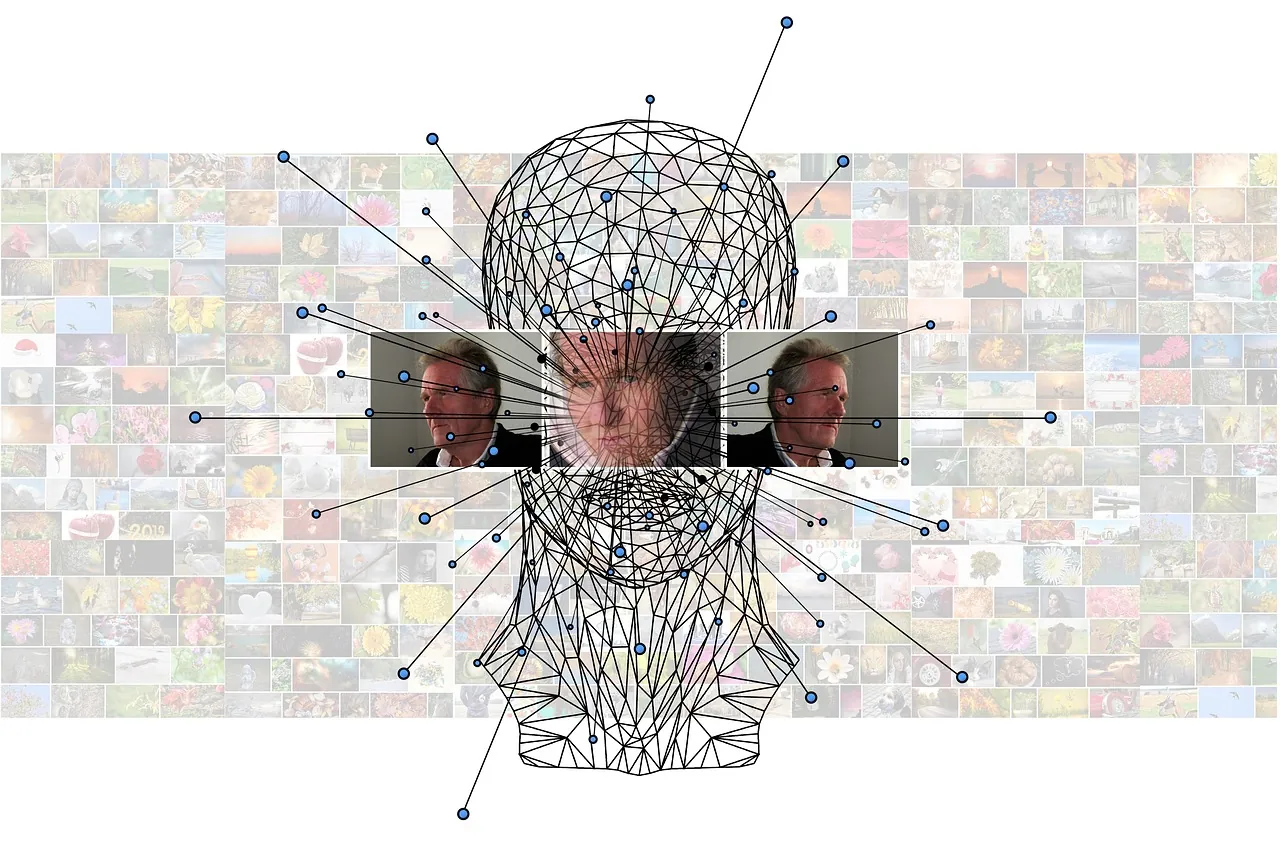
Understanding Machine Learning Algorithms
Machine learning (ML) algorithms, especially those leveraging neural networks, can process and learn from data in ways that mimic human cognitive functions. These algorithms are particularly adept at handling large datasets and can be used to develop models that predict potential threats based on historical attack data.
Types of Algorithms Used in Cybersecurity
- Supervised Learning: Utilized for training models on labeled datasets to identify known threats.
- Unsupervised Learning: Useful for detecting unknown anomalies by grouping similar events and recognizing deviations.
- Reinforcement Learning: Enables systems to learn optimal defense strategies through trial and error in simulated environments.
Integrating AI with Existing Security Systems
Integrating AI into existing security frameworks involves several key steps. These include identifying the right ML models, ensuring data integrity, and developing a cohesive system architecture.
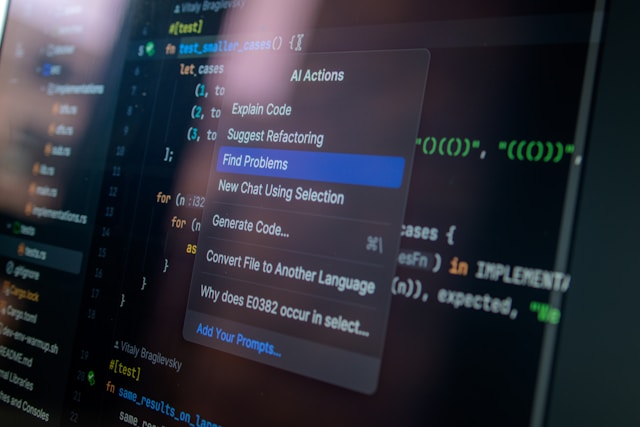
Step-by-Step Integration Framework
1. Assess Current Security Infrastructure
Begin by evaluating your current cybersecurity setup. Identify gaps that AI could fill, such as areas prone to human error or requiring constant monitoring.
2. Define Clear Objectives
Set clear goals for what you aim to achieve with AI integration. Whether it's reducing response times or improving detection accuracy, having defined objectives will guide your implementation strategy.
3. Data Collection and Preprocessing
AI systems rely on high-quality data. Ensure that your data collection methods are robust and that datasets are preprocessed to eliminate noise and redundancies.
4. Select Appropriate ML Models
Select models that best suit your needs. For instance, use deep learning for complex pattern recognition tasks, while logistic regression might suffice for more straightforward classification problems.
5. Develop a Seamless System Architecture
Create an architecture that allows seamless communication between AI tools and existing systems. This could involve integrating APIs or using middleware solutions to bridge any technological gaps.
6. Implement and Test
Once integrated, rigorously test the system under various scenarios to ensure reliability and effectiveness. Use simulations to evaluate how the system responds to different types of attacks.
Real-World Applications and Case Studies
Numerous organizations have successfully implemented AI for real-time threat detection. One notable example is a leading financial services firm that reduced its response time to security incidents by 60% within a year of adopting AI-driven threat intelligence tools.
Case Study: AI in the Financial Sector
A multinational bank faced challenges with increasing phishing attacks targeting its customers. By deploying an AI-powered security platform, the bank could scan millions of emails in real-time, identifying and blocking potential threats before they reached end-users.
- Outcome: The solution reduced false positives by 30% and helped maintain customer trust by preventing breaches proactively.
Challenges and Considerations
While AI offers significant advantages, its implementation is not without challenges. Organizations must navigate issues like data privacy concerns, the risk of model bias, and the need for continuous model training.
Managing Data Privacy
AI systems require access to extensive data sets, raising privacy concerns. Adopting strategies like anonymization and secure data storage can mitigate these risks while complying with regulations like GDPR.
Ensuring Fairness and Reducing Bias
Bias in AI models can lead to unfair outcomes. Continuous monitoring and updating of models are necessary to ensure fairness and accuracy in threat detection.
The Future of AI in Cybersecurity
The future landscape of cybersecurity will be heavily influenced by AI advancements. As AI technologies evolve, we can expect even more sophisticated tools capable of predicting and neutralizing threats with greater precision.
Organizations adopting these innovations early stand to gain a significant advantage in protecting their digital assets against the ever-evolving threat landscape.