Understanding the Cybersecurity Landscape for Remote Work
The transition to remote work has brought about a paradigm shift in how businesses operate, but it has also introduced a plethora of cybersecurity challenges. The rise in cyberattacks during the COVID-19 pandemic highlighted vulnerabilities as more employees connected to corporate networks from home.
Securing these dispersed networks requires more than traditional perimeter defenses. To effectively protect remote workers, companies need comprehensive strategies that encompass employee training, secure access protocols, and continuous monitoring. In this article, we'll explore actionable strategies tailored to remote work environments, focusing on these three critical areas.
Assess Current Security Practices
The first step in strengthening your cybersecurity posture is understanding your current landscape. Conducting a thorough assessment of your existing security practices will help identify gaps and opportunities for improvement.
Conducting a Security Audit
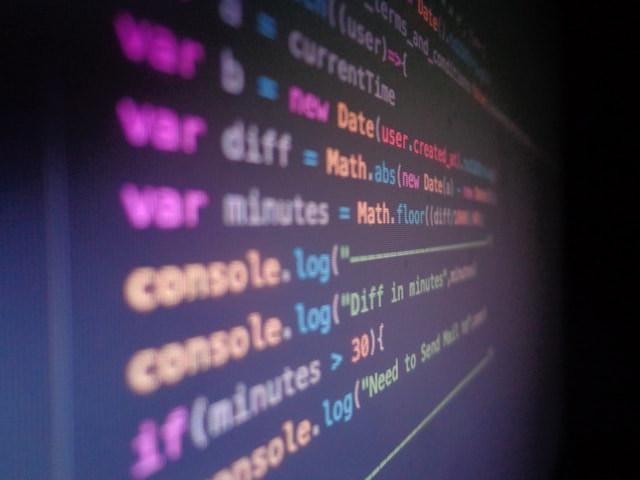
A comprehensive security audit can uncover vulnerabilities in your current setup. Start by reviewing your network configurations, firewall settings, and endpoint protections. Are all devices updated with the latest security patches? Are there any unused accounts or open ports that could pose risks?
Consider engaging an external security firm to conduct penetration testing. This simulated cyberattack can expose weak points that an internal audit might miss.
Employee Surveys
Your employees are on the front lines and often know best where potential issues may lie. Conduct anonymous surveys to gather feedback on their security concerns and experiences. Ask questions like:
- How confident are you in recognizing phishing attempts?
- Do you feel adequately trained in using security tools?
- What challenges do you face when accessing company resources remotely?
Implement Role-Based Access Controls (RBAC)
Once you've assessed the current practices, the next step is implementing robust access control measures. Role-Based Access Controls (RBAC) ensure that employees have access only to the information necessary for their job functions, minimizing potential damage from compromised accounts.
Defining Roles and Permissions
Create a matrix of roles within your organization, detailing the specific permissions each role requires. For example, a marketing team member might need access to social media platforms but not financial data.
This segmentation limits the scope of access and helps contain any security breaches to a smaller subset of data and applications.
Enforcing Least Privilege
The principle of least privilege dictates that users should have the minimum level of access—or permissions—necessary to perform their job functions. Regularly review user permissions and adjust them as roles change or employees leave the company.
Automating these reviews with identity management software can streamline the process and ensure that outdated permissions do not linger unnoticed.
Train Employees on Recognizing Phishing Attempts
Human error remains one of the leading causes of cybersecurity breaches, making employee training an essential component of your defense strategy. A well-informed workforce is a critical line of defense against phishing and other social engineering attacks.
Developing a Training Program
Create a structured training program that covers key topics such as:
- Recognizing suspicious emails and links
- Understanding the importance of secure password practices
- Using multi-factor authentication effectively
Interactive workshops and webinars can engage employees better than passive e-learning modules, making them more likely to retain information.
Simulated Phishing Attacks
Conduct regular simulated phishing attacks to test your team's readiness and reinforce training lessons. Analyze results to identify areas for improvement and offer additional support where needed.
Tools like KnowBe4 or PhishMe provide platforms for these simulations and can track metrics such as click rates on phishing emails and report rates by employees.
Enhancing Secure Access Protocols
As remote work continues to blur the lines between personal and professional environments, it's crucial to establish secure access protocols for connecting to company resources.
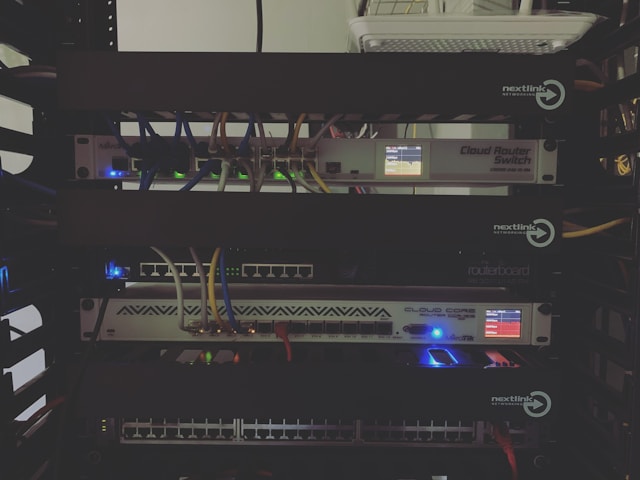
Virtual Private Networks (VPNs)
A Virtual Private Network encrypts internet traffic, providing a secure connection to corporate networks from remote locations. Ensure all remote employees use a company-approved VPN service to safeguard data transmission over public or less-secure home networks.
Zero Trust Architecture
The Zero Trust model assumes that threats can come from both outside and inside the network. It requires strict identity verification for every person and device trying to access resources, regardless of whether they are inside or outside the corporate network.
Implementing Zero Trust can be complex but rewarding, providing a more resilient defense against unauthorized access.
Continuous Monitoring and Response
No security measure is foolproof, which is why continuous monitoring is vital. Setting up real-time alerts for suspicious activities enables prompt responses to potential threats.
Endpoint Detection and Response (EDR)
EDR solutions provide visibility into endpoints, detecting malicious activities as they occur. They collect data from devices such as laptops and smartphones, allowing IT teams to investigate incidents quickly.
Security Information and Event Management (SIEM)
SIEM tools aggregate logs from various sources, analyzing them for signs of anomalous behavior. These platforms facilitate threat detection, compliance reporting, and incident response coordination.
Conclusion
The shift to remote work has created unique cybersecurity challenges that demand equally unique solutions. By assessing current security practices, implementing RBAC, training employees on phishing recognition, enhancing secure access protocols, and establishing continuous monitoring systems, companies can protect their teams from the myriad threats posed by home environments.
The path to robust cybersecurity is ongoing and dynamic; staying ahead requires continual adaptation and vigilance. As the digital landscape evolves, so too must our strategies for securing it.