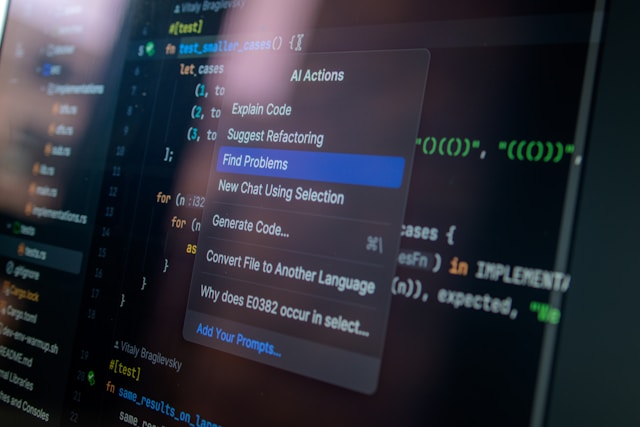
Understanding the Importance of Cyber Hygiene
Cyber hygiene refers to the basic steps that organizations take to maintain system health and improve online security. For small businesses, implementing a robust cybersecurity protocol can seem daunting. However, establishing strong cyber hygiene is not just a necessity but a strategic advantage. Small businesses often lack the extensive IT resources of larger organizations, making them attractive targets for cybercriminals. By following essential cybersecurity practices, you can protect your business from potential threats and data breaches.
Implementing Regular Software Updates
One of the most straightforward yet critical steps in improving cybersecurity is keeping all software up-to-date. Software updates often contain patches for vulnerabilities that could be exploited by hackers. An example would be the infamous WannaCry ransomware attack in 2017, which affected systems running outdated versions of Windows.
Automated Update Scheduling
Many operating systems and applications allow you to schedule automatic updates. Setting these to occur during off-peak hours can minimize disruptions to your operations. For Windows users, enabling 'Automatic Updates' ensures the system installs security patches as soon as they are released.
Employee Training on Phishing Awareness
Phishing attacks remain one of the most common methods for cybercriminals to gain unauthorized access to information. Training employees to recognize phishing emails is crucial in maintaining cybersecurity.
Conducting Regular Workshops
Small businesses should hold quarterly workshops to educate employees about the latest phishing tactics. Provide examples of phishing attempts, highlighting red flags such as misspelled domain names, suspicious attachments, and unsolicited requests for sensitive information.
- Interactive Training Modules: Utilize interactive modules that simulate phishing attacks and provide immediate feedback.
- Gamified Learning: Introduce gamification elements, like quizzes and badges, to make learning engaging and effective.
Establishing Strong Password Policies
Password security is often overlooked but is a critical aspect of protecting business data. Implementing a strong password policy within your organization helps prevent unauthorized access.
Password Management Tools
Encourage the use of password managers, such as LastPass or Bitwarden, which help employees generate and store complex passwords securely. A strong password typically includes a mix of uppercase letters, lowercase letters, numbers, and symbols.
Utilizing Multi-Factor Authentication (MFA)
MFA provides an additional layer of security beyond just passwords. It typically requires two or more verification methods such as a code sent to a mobile device, a fingerprint scan, or a facial recognition step.
Implementing MFA Across Applications
Ensure that all critical systems and applications support MFA. Popular services like Google Workspace and Microsoft 365 offer built-in MFA options that are easy to set up and manage.
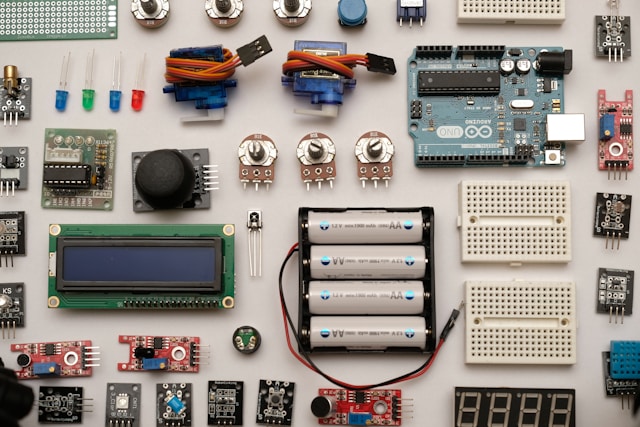
Regular Data Backups
A comprehensive backup strategy ensures that your business can recover from data loss incidents like cyberattacks or hardware failures. Backups should be frequent and stored securely.
Choosing the Right Backup Solution
For small businesses, cloud-based backup solutions such as Acronis or Backblaze offer reliability and scalability. It is essential to perform backups at least once a week and keep copies offsite in a secure location.
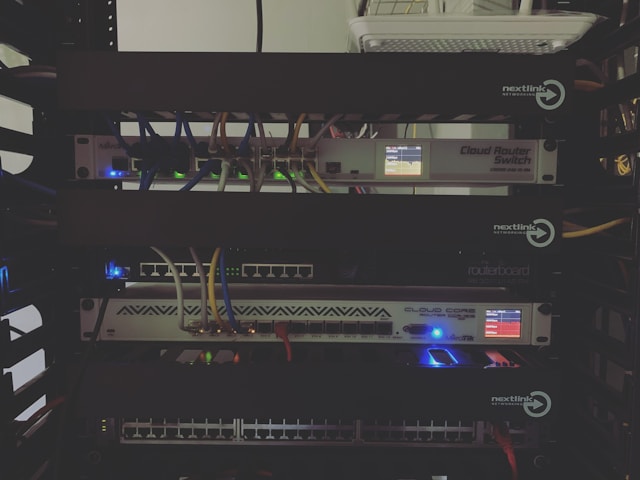
Network Security Measures
Your network is often the first line of defense against cyber threats. Implementing network security measures helps protect sensitive data as it travels through your infrastructure.
Installing Firewalls
A firewall monitors incoming and outgoing network traffic based on predetermined security rules. Most modern operating systems come with built-in firewalls; however, it's advisable to install additional hardware-based firewalls for added protection.
- Network Segmentation: Divide your network into segments to limit access to sensitive areas and minimize the impact of breaches.
- Secure Wi-Fi: Ensure Wi-Fi networks are encrypted (WPA3) and hidden from public view by disabling SSID broadcasting.
Conducting Regular Security Audits
Security audits involve a thorough review of your systems and practices to identify vulnerabilities and areas for improvement. They are vital in maintaining up-to-date security protocols.
Hiring Professional Services
Consider hiring cybersecurity professionals to perform audits and vulnerability assessments regularly. These experts can provide insights into potential weaknesses you may have overlooked.
Cybersecurity Insurance
As cyber threats become more sophisticated, having cybersecurity insurance can provide financial protection against losses due to data breaches or other cybersecurity incidents.
Selecting the Right Policy
When choosing cybersecurity insurance, ensure it covers key areas such as data breaches, system failure, and extortion demands. Consult with a broker who specializes in cyber insurance for small businesses to find the best coverage for your needs.
Cultivating a Security-First Culture
Ultimately, fostering an organizational culture that prioritizes security is essential. Employees should understand that cybersecurity is everyone's responsibility—not just the IT department's.
Promoting Security Awareness
Create a security awareness program that includes regular communications from leadership highlighting the importance of cybersecurity practices. Celebrate achievements and share stories of successful threat mitigations within the company.
By incorporating these essential steps into your daily operations, small businesses can significantly improve their cybersecurity posture. Each measure builds upon the last, creating a multi-layered defense system designed to protect against increasingly complex cyber threats.