Understanding the Cybersecurity Landscape for Small Businesses
Small enterprises often underestimate the importance of robust cybersecurity measures, believing they are too small to attract the attention of hackers. However, statistics show that 43% of cyberattacks target small businesses. The impact can be devastating, with 60% of small businesses closing within six months of a data breach. Therefore, it's crucial for small business owners to prioritize data protection.
Identifying Potential Threats
The first step in strengthening data protection protocols is understanding the types of threats your business might face. These include:
- Phishing Attacks: Fraudulent attempts to obtain sensitive information such as usernames and passwords by masquerading as trustworthy entities.
- Ransomware: Malicious software that encrypts files on a victim's system and demands a ransom for the decryption key.
- Insider Threats: Employees or contractors who misuse their access to business data.
Recognizing these threats allows businesses to tailor their defense mechanisms effectively.
Creating a Threat Assessment Workflow
To combat potential threats, small businesses should establish a threat assessment workflow. Here's an example:
- Risk Identification: Compile a list of digital assets and assess their vulnerability to potential threats.
- Impact Analysis: Evaluate the potential consequences of a breach for each asset, including financial losses and reputational damage.
- Risk Mitigation Strategies: Implement solutions such as encryption, multi-factor authentication (MFA), and regular software updates.
Implementing Effective Policies
A comprehensive cybersecurity policy is essential. It provides guidelines and sets expectations for employees regarding the handling of sensitive data. Key components include:
Password Management
Enforce a strict password policy, requiring employees to create strong passwords that are updated regularly. Utilize password management tools to store and manage these securely.
Access Controls
Implement role-based access controls (RBAC) to ensure employees have access only to the data necessary for their roles. This minimizes the risk of data exposure from insider threats.
Data Encryption
Encrypt sensitive data both at rest and in transit. This ensures that even if data is intercepted, it remains unreadable to unauthorized users.
Regular Audits
Conduct regular security audits to identify vulnerabilities and ensure compliance with the latest cybersecurity standards.
Cultivating a Culture of Security Awareness
The human factor is often the weakest link in cybersecurity. Fostering a culture of security awareness among employees can greatly enhance data protection protocols.
Employee Training Programs
Develop comprehensive training programs that educate employees on recognizing phishing attempts, secure data handling practices, and the importance of reporting suspicious activities.
An effective training program includes:
- Interactive Workshops: Engage employees through simulations of common cyber threats.
- Regular Updates: Provide ongoing education on emerging threats and trends in cybersecurity.
Encouraging Reporting
Create an environment where employees feel comfortable reporting suspicious activities without fear of reprisal. Establish clear reporting procedures and ensure all reports are investigated promptly.
Selecting the Right Tools and Technologies
While policies and training are crucial, implementing the right tools can bolster your cybersecurity framework.
Firewall and Antivirus Solutions
A robust firewall serves as your first line of defense against external attacks, while up-to-date antivirus software helps detect and neutralize malware before it can cause harm.
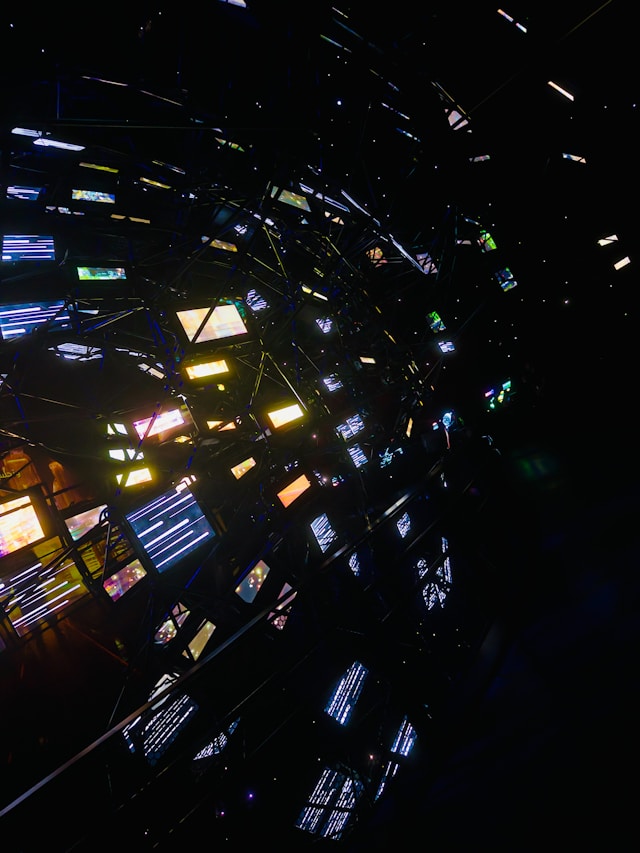
Security Information and Event Management (SIEM)
SIEM systems aggregate and analyze security data from across your network, providing real-time analysis of security alerts generated by applications and network hardware.
Backup Solutions
Regular backups are vital in ensuring business continuity in case of a ransomware attack or data loss. Automate backups and verify their integrity regularly.
Balancing Budget Constraints with Cybersecurity Needs
Small businesses often operate under tight budget constraints. However, investing in cybersecurity should be viewed as a necessity rather than an optional expense. Consider the following approaches:
- Cloud-Based Solutions: Many cloud service providers offer integrated security features that can be more cost-effective than building in-house solutions.
- Open Source Tools: Leverage open-source cybersecurity tools that are free or low-cost, such as Snort for intrusion detection or OpenVPN for secure remote access.
The key is to prioritize investments based on the potential impact on your business operations and client trust.
The Role of Cybersecurity Insurance
An additional layer of protection comes in the form of cybersecurity insurance. It can cover the costs associated with a data breach, including legal fees, notification expenses, and compensation for affected parties. Evaluate policies based on your specific risks and ensure adequate coverage.
The Future of Cybersecurity for Small Enterprises
The cybersecurity landscape is constantly evolving. As new threats emerge, so too must our defenses. Small businesses should stay informed about technological advancements and update their protocols accordingly.
This proactive approach not only protects valuable data but also enhances trust among clients and partners, ultimately contributing to business success and longevity.