The Rising Tide of Cyber Threats in Healthcare
In recent years, healthcare institutions have increasingly found themselves in the crosshairs of cybercriminals. These attacks range from data breaches that expose sensitive patient information to ransomware incidents that can cripple hospital operations. The stakes are high, as the impact of a successful cyberattack can extend beyond financial loss to erode patient trust and jeopardize lives.
According to a report by the Ponemon Institute, healthcare organizations incur the highest costs associated with data breaches, averaging $7.13 million per incident. Moreover, the sector is seeing a surge in both the frequency and sophistication of cyberattacks, as malicious actors realize the value and vulnerability of healthcare data.
Case Study: The WannaCry Attack on NHS
One of the most notorious examples of a cyberattack on a healthcare institution is the 2017 WannaCry ransomware attack. This global incident severely impacted the UK's National Health Service (NHS), leading to widespread operational disruption.
The attack was notable not only for its scale but also for its impact. Over 19,000 appointments were canceled, and numerous hospitals were forced to divert emergency patients due to IT system failures. While WannaCry was eventually contained, it highlighted significant weaknesses in cybersecurity protocols across healthcare systems.
The NHS's response included strengthening its cybersecurity infrastructure through investments in advanced threat detection systems and rigorous staff training programs. This proactive approach has since become a template for other healthcare providers globally.
Impact on Patient Trust and Operational Continuity
Cybersecurity breaches in healthcare do more than just compromise patient data; they undermine trust in medical institutions. Patients expect their personal and medical information to be kept confidential and secure. A breach can lead to identity theft, financial fraud, and even endanger patient safety if medical records are altered or unavailable during treatment.
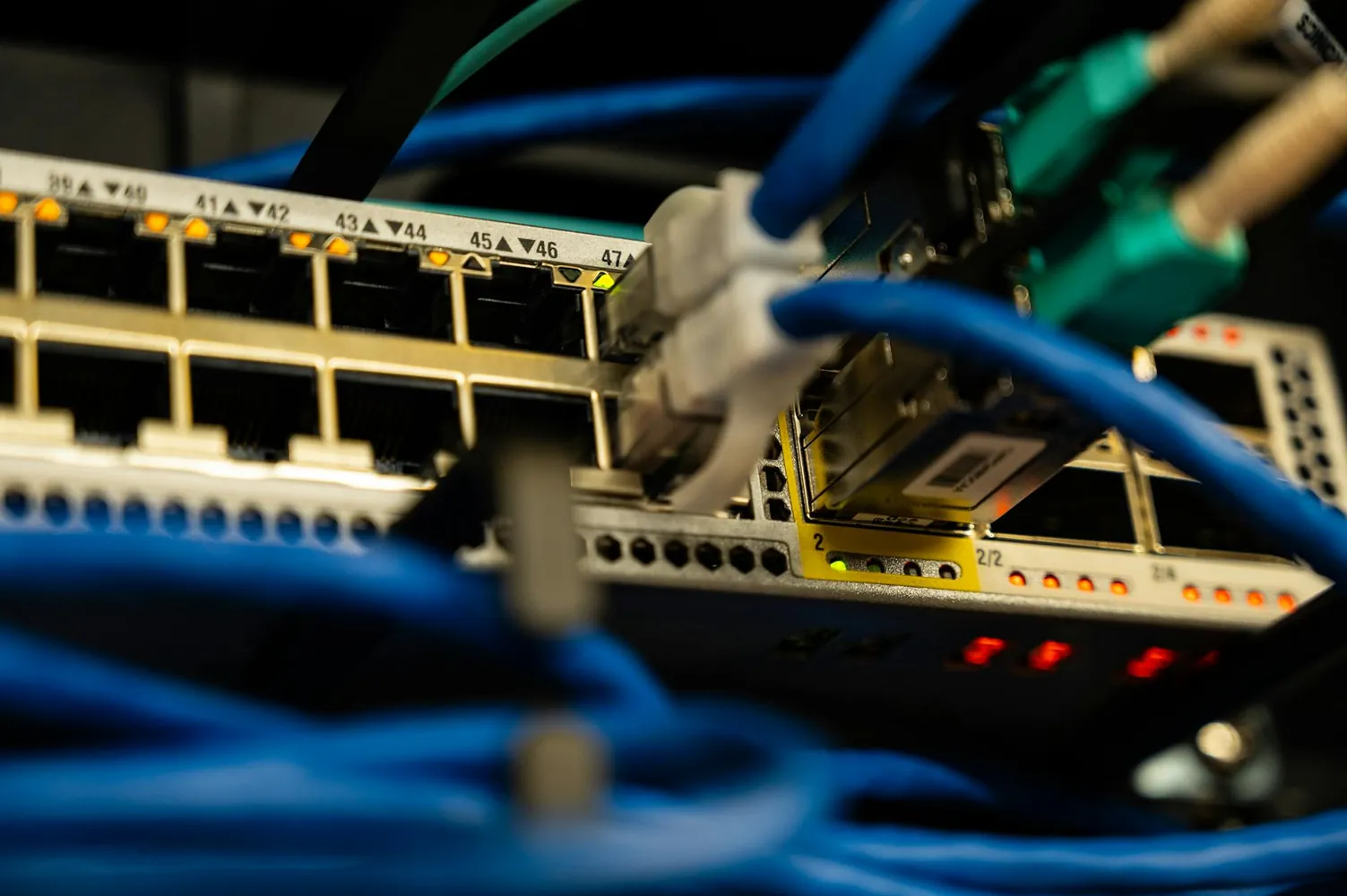
Operational continuity is another critical concern. Hospitals rely heavily on digital systems for everything from patient records management to medical device operation. A cyberattack that disrupts these systems can halt surgeries, delay diagnoses, and even force hospitals to close temporarily.
Strategic Recovery and Defense Strengthening
Recovering from a cyberattack involves more than just restoring systems; it requires a strategic overhaul of cybersecurity practices. Healthcare institutions often undertake the following steps:
- Incident Response Plan (IRP): Developing and continuously updating an IRP helps organizations respond swiftly and effectively to attacks. This plan should include roles and responsibilities, communication strategies, and steps for containment and recovery.
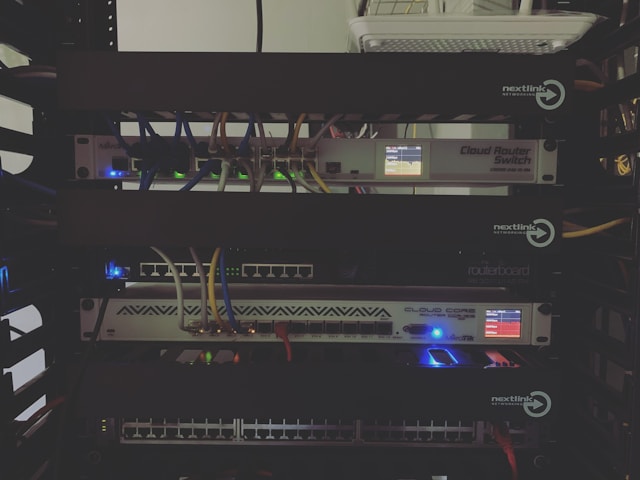
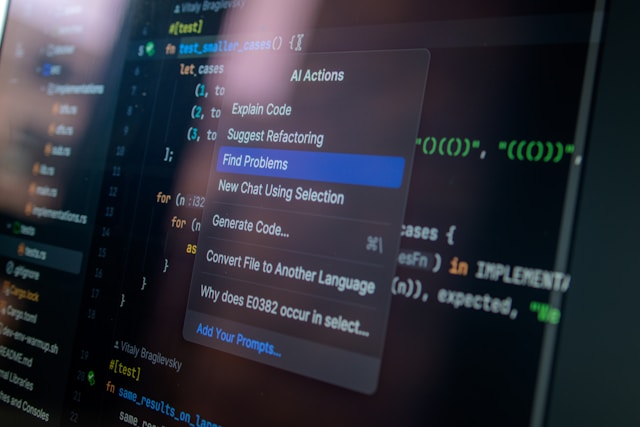
- Investment in Advanced Security Technologies: Technologies such as intrusion detection systems, endpoint protection platforms, and artificial intelligence-driven anomaly detection can help identify threats before they escalate.
- Regular Security Audits: Conducting regular audits ensures that security measures are current and effective against new vulnerabilities.
- Employee Training Programs: Human error remains a significant cybersecurity risk factor. Regular training on recognizing phishing attacks and secure data handling practices is crucial.
Example Workflow for Strengthening Defenses
A typical workflow for a healthcare institution aiming to bolster its cybersecurity defenses might include the following steps:
- Conduct a comprehensive risk assessment to identify vulnerabilities in existing systems.
- Prioritize risks based on potential impact and likelihood of occurrence.
- Deploy advanced security solutions tailored to identified vulnerabilities, ensuring interoperability with existing IT infrastructure.
- Implement continuous monitoring systems to detect and respond to threats in real-time.
- Regularly review and update security policies and procedures to reflect the evolving threat landscape.
The Role of Collaboration and Regulation
Collaboration among healthcare providers, government agencies, and cybersecurity experts is critical in developing effective defense strategies. Initiatives like the Healthcare Information Sharing and Analysis Center (H-ISAC) facilitate the sharing of threat intelligence and best practices among stakeholders.
Regulation also plays a key role in enhancing cybersecurity resilience. In the US, the Health Insurance Portability and Accountability Act (HIPAA) sets standards for safeguarding patient information. More recently, efforts have been made to introduce frameworks like the Cybersecurity Act of 2015, which encourages voluntary sharing of cyber threat indicators among entities.
The Future of Cybersecurity in Healthcare
As healthcare continues to digitize, the importance of robust cybersecurity measures cannot be overstated. Emerging technologies such as blockchain for secure data exchanges, biometric authentication methods for access control, and quantum cryptography for data encryption are being explored as potential game-changers in enhancing security.
Ultimately, the challenge of cybersecurity threats in healthcare is an ongoing battle requiring constant vigilance, adaptation, and innovation. By learning from past incidents and embracing cutting-edge solutions, healthcare institutions can safeguard their systems, protect patient trust, and ensure seamless operational continuity.