Understanding Behavioral Analysis in Cybersecurity
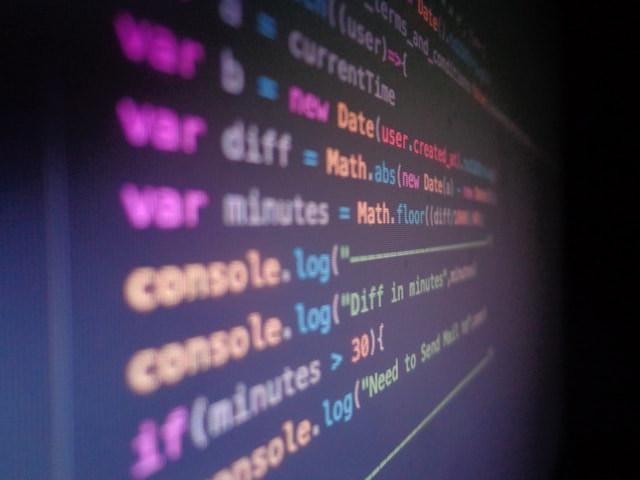
Behavioral analysis is an increasingly prominent approach in cybersecurity, particularly for identifying insider threats. Unlike traditional threat detection systems that rely on known signatures or predefined rules, behavioral analysis focuses on detecting anomalies in user behavior. This method leverages machine learning and advanced analytics to establish baselines of normal activity and then flags deviations that may indicate malicious intent.
The core strength of this approach lies in its ability to uncover unknown threats. However, implementing behavioral analysis requires a nuanced understanding of both its potential benefits and its limitations.
Practical Methods for Identifying Insider Threats
User Behavior Analytics (UBA)
User Behavior Analytics (UBA) involves monitoring the actions of users within a network to detect abnormal behavior patterns. By establishing a profile of what constitutes 'normal' behavior for each user, organizations can detect anomalies that suggest potential security risks.
- Baseline Activity: UBA tools create a profile based on historical data, such as login times, file access patterns, and frequency of data transfers.
- Anomaly Detection: Any deviation from the established baseline triggers alerts for further investigation.
For example, if an employee who typically accesses financial data during business hours suddenly downloads large amounts of data at midnight, UBA systems will flag this as suspicious.
Incident Response Planning
Effective incident response planning is crucial to mitigate the impact of detected threats. It involves developing structured protocols to respond to potential insider threats swiftly and efficiently.
- Preparation: Establish roles and responsibilities for team members during a security incident.
- Detection and Analysis: Use UBA alerts to guide analysis and determine the scope of the threat.
- Containment, Eradication, and Recovery: Implement measures to contain the threat, eradicate the root cause, and restore normal operations.
Consider a scenario where an employee accesses sensitive files from an unauthorized location. An effective response plan would involve isolating the affected system, analyzing the extent of the breach, and determining whether data exfiltration occurred.
Employee Education
Education plays a vital role in preventing insider threats. Employees are often the first line of defense against cyber threats, so it's essential that they understand the importance of data security and recognize signs of potential breaches.
- Regular Training Sessions: Conduct workshops on recognizing phishing attempts, social engineering tactics, and safe internet practices.
- Security Awareness Campaigns: Use newsletters and alerts to keep security top-of-mind for all employees.
A case study involving a mid-sized tech company highlights the impact of training. After implementing quarterly cybersecurity training sessions, the company saw a 40% reduction in successful phishing attacks within one year.
Strengths of Behavioral Analysis
Proactive Threat Detection
One of the key advantages of behavioral analysis is its proactive nature. Traditional security measures often rely on databases of known threats, which limits their effectiveness against new or evolving attack vectors. In contrast, behavioral analysis can detect suspicious activity regardless of whether it matches a known signature.
Adaptability
Behavioral analysis systems are highly adaptable. They can evolve by learning from new data, improving accuracy over time. This adaptability is crucial in a constantly changing threat landscape where cyberattack techniques rapidly evolve.
Weaknesses of Behavioral Analysis
High False Positive Rate
A common challenge with behavioral analysis is its tendency to produce false positives. Because these systems alert on any deviation from established norms, benign anomalies can trigger unnecessary alarms. For instance, an employee accessing work systems while traveling might be flagged as suspicious without malicious intent.
Complexity in Implementation
Implementing behavioral analysis requires significant resources. Organizations must invest in sophisticated software, skilled personnel, and ongoing system tuning to maintain accuracy. Additionally, collecting and analyzing vast amounts of user data raises privacy concerns that need careful handling to comply with regulations like GDPR.
Integrating Behavioral Analysis with Other Security Measures
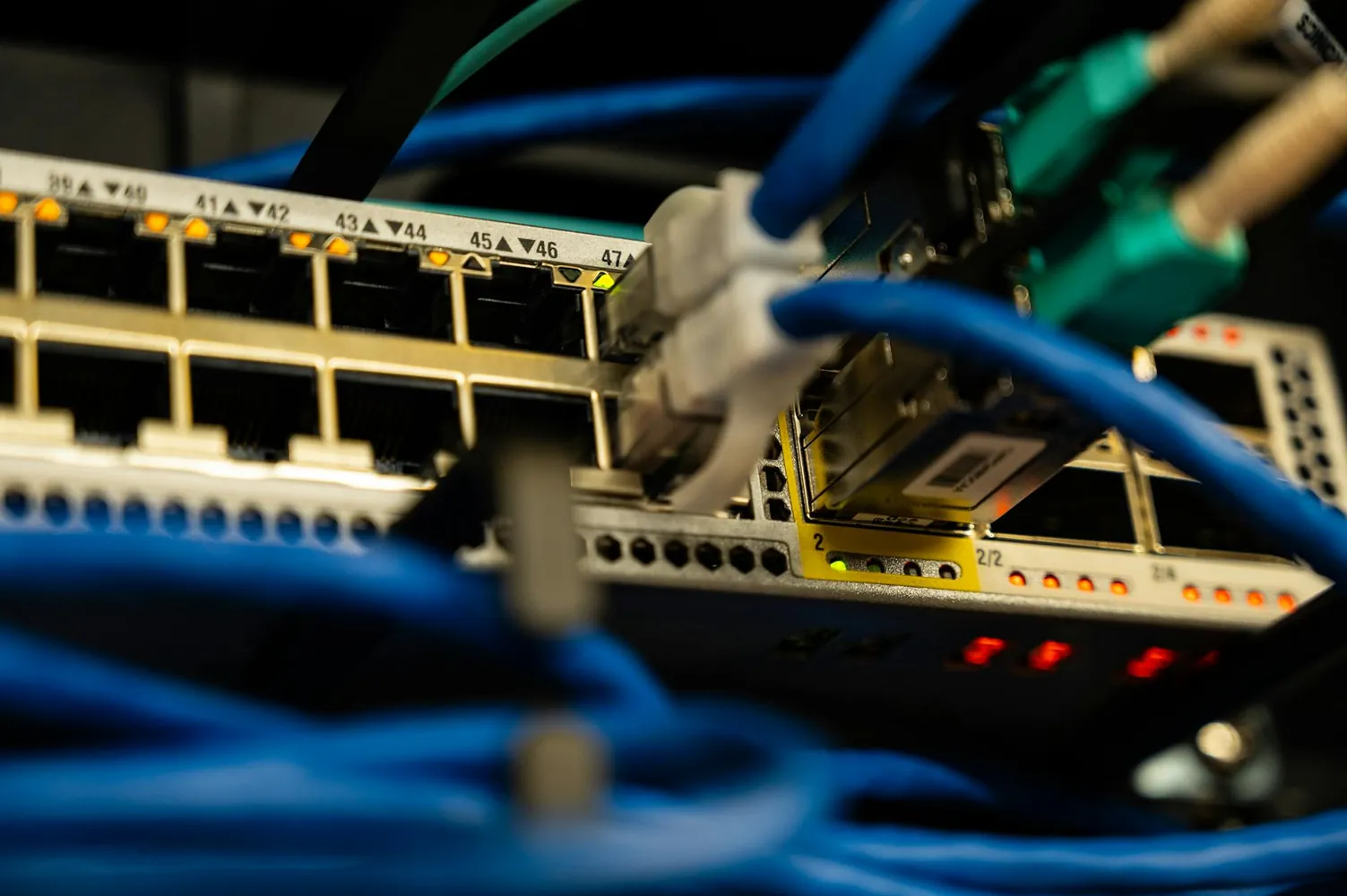
While behavioral analysis is powerful, it works best when integrated with other security strategies. A multi-layered approach enhances overall protection by combining different technologies and methodologies.
- Combining with Signature-Based Detection: While behavioral analysis excels at identifying unknown threats, signature-based systems remain effective against known malware.
- Utilizing Network Traffic Analysis: Monitoring network traffic patterns can provide additional context to user behavior anomalies.
This holistic approach creates a comprehensive security posture capable of addressing diverse threat vectors more effectively than any single method alone.
Conclusion
Behavioral analysis represents a cutting-edge approach to cybersecurity, offering substantial benefits in identifying potential insider threats. By leveraging machine learning and analytics, organizations can proactively detect anomalies indicative of malicious activity. However, understanding its limitations—such as high false positive rates and implementation complexity—is crucial for effective deployment.
A balanced strategy that integrates behavioral analysis with other security measures, coupled with robust incident response planning and employee education, provides the best defense against evolving cyber threats.